Latest Blogs

By AMSAT Oct 25,2023
The Evolution of Security Operation Centers: Adapting to Modern Cyber Threats
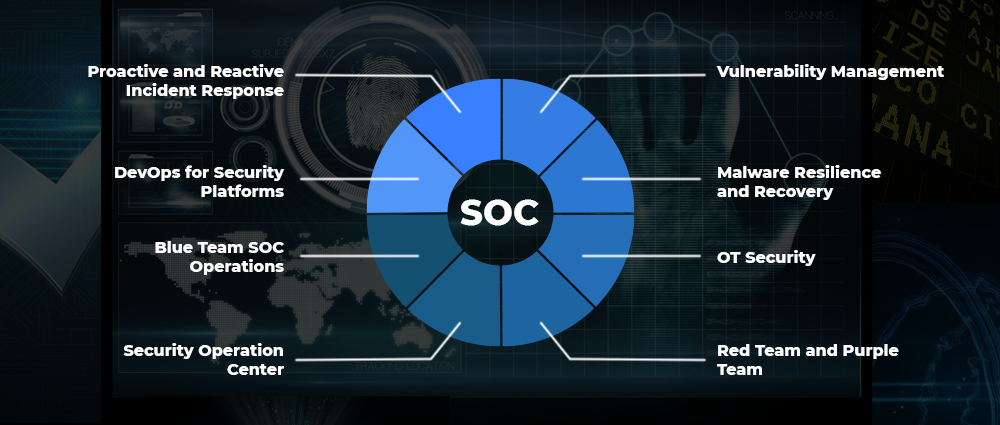
Security Operation Centers, or SOCs, are key to securing organizations against malicious cyberattacks. Therefore, enterprises, regardless of size, must adopt strategies and techniques to outsmart ingenious threat actors. In fact, a resilient SOC is extremely difficult without effective monitoring, incident response capabilities, and proactive threat intelligence integration. In addition, to ensure robust cybersecurity defence, the importance of developing collaboration, leveraging innovative tools, and emphasizing employee training cannot be overemphasized.
Evolution of SOCs
SOCs have evolved significantly over the years, thanks to technological advancements and fast-changing threat landscape. Early SOCs focused on perimeter defense, relying heavily on firewalls and intrusion detection systems. They primarily reacted to known threats.
As threats became more sophisticated and organizations began to adopt new technologies, SOCs needed to evolve to keep up. Next-generation SOCs focus on proactive threat detection and response, leveraging a variety of tools and technologies, including security information and event management, threat intelligence, and security orchestration, automation, and response (SOAR) platforms.
Modern Cyber Threats
Modern cyber threats are becoming increasingly inventive and dangerous, posing a major challenge to individuals, organizations, and governments across the globe. These threats can take many forms, including malware, phishing attacks, ransomware, and denial-of-service attacks. They can be used to steal sensitive data, disrupt operations, or extort money.
One of the most common cyber threats is malware, which is malicious software that can damage or disable computer systems or steal data. Malware can be spread through a variety of means, including email attachments, malicious websites, and USB drives. Phishing attacks are another common cyber threat. They involve sending fraudulent emails or text messages that appear to be from a legitimate source, such as a bank or credit card company.
Ransomware is a type of malware that encrypts a victim’s files and demands a ransom payment in exchange for the decryption key. Ransomware attacks have become increasingly common in recent years, and they have been used to target businesses of all sizes, as well as individuals.
Denial-of-service attacks are another type of cyber-attack that can be used to disrupt operations or extort money. Denial-of-service attacks involve flooding a website or server with traffic, making it unavailable to legitimate users.

Adapting to Modern Cyber Threats
SOCs must adapt to modern cyber threats by adopting a proactive approach to security. This means using a variety of tools and technologies to detect and respond to threats quickly and effectively.
Here are some key steps that SOCs can take to adapt to modern cyber threats:
- Implement a SIEM system: A SIEM system is essential for collecting and analyzing data from a variety of security sources to identify suspicious activity.
- Use threat intelligence: Threat intelligence can help SOCs to stay ahead of attackers and identify potential threats before they strike.
- Automate tasks: SOCs can automate tasks such as incident response and threat hunting to free up analysts to focus on more complex tasks.
- Build a team of skilled analysts: SOCs need a team of skilled analysts who can understand and respond to the latest threats.
Security Operations Center SIEM Use Cases and Cyber Threat Intelligence
SIEM systems and cyber threat intelligence play a vital role in SOCs. SIEM systems can be used to detect and respond to a variety of threats, including APTs, ransomware, phishing attacks, and supply chain attacks.
Cyber threat intelligence can be used to improve the effectiveness of SIEM systems by providing information about the latest threats, vulnerabilities, and attack techniques. This information can be used to create rules and alerts that will help SIEM systems to identify suspicious activity.
SOC Service
SOC services can provide a number of benefits to organizations, including:
- Reduced costs: SOC services can help organizations save money on the costs of building and maintaining their own SOCs.
- Improved security: SOC services can help organizations improve their security posture by providing access to experienced security analysts and the latest tools and technologies.
- Reduced workload: SOC services can help organizations to reduce the workload on their IT staff by taking care of security monitoring and response.
SOC for Cybersecurity
The role of SOCs in cybersecurity is highly critical. SOCs help secure organizations from a variety of attacks by monitoring and responding to cyber threats.
Here are some of the key benefits of having a SOC for cybersecurity:
- Reduced risk of cyberattacks: SOCs can help organizations cut their risk of cyberattacks by identifying and responding to threats quickly and effectively.
- Improved compliance: SOCs can help organizations comply with security regulations and standards.
- Reduced costs: SOCs can help organizations save money on the costs of recovering from cyberattacks.
Conclusion
Security Operations Centers (SOCs) have seen rapid evolution over the last few years, adapting to the ever-changing threat landscape. Once chiefly focused on reactive incident response, modern SOCs now employ a proactive approach, using intelligence, automation, and collaboration to secure organizations from a wide range of cyber threats.
TAGS
- Cyber Threats
- Security Operations Centers
- Threat Intelligence
Recent Blogs
Ready to Get Started?
Our specialists are ready to tailor our security service solutions to fit the needs of your organization.











One thought on “The Evolution of Security Operation Centers: Adapting to Modern Cyber Threats”