By AMSAT March 26, 2026
Information Security Risk Management: Complete Guide for 2026
A single breach can unravel years of trust. That’s why information security risk management has moved from a back-office IT concern to a fundamental pillar of how modern businesses operate.
Cyber threats aren’t slowing down. Ransomware groups now run like businesses. AI is making phishing attacks harder to spot. And regulators across the US, EU, and beyond are no longer treating cybersecurity as optional; formal risk management programs are now a legal requirement in many industries.
Whether you’re a startup handling your first batch of customer data or an enterprise running infrastructure that thousands rely on, the cost of ignoring security risks is real. Financial losses, regulatory penalties, and a reputation that takes years to rebuild are all on the table.
This guide walks you through everything you need to know about building an effective IT security risk management program in 2026 and beyond, the frameworks, the process, and the strategies that make it work.
What you’ll learn:
- What information security risk management is and why it matters in 2026
- How to assess your organization’s current ISRM maturity level and what each stage means for your security posture.
- The 5 core stages of an ISRM program: from identification to review.
- The step-by-step ISRM process: from asset identification to continuous monitoring.
- The top frameworks include NIST RMF, ISO 27005, and FAIR.
- The fundamental objectives of information security and the CIA triad.
- How to handle third-party risk management.
- How to integrate ISRM into your broader enterprise risk management strategy.
- How to build your ISRM program with a practical roadmap.
- How to measure your ISRM program.
What Is Information Security Risk Management?
Information security risk management (ISRM) is the evolving process of identifying, assessing, treating, and monitoring risks to your organization’s information assets. Those risks can come from outside, like cybercriminals, hackers, and nation-state actors, or from within, like a misconfigured system or a simple human mistake.
Every information security and risk management program starts with three questions:
- What potential issues could arise?
- What is the probability of these issues occurring, and what would be the consequences?
- How will we respond to these risks?
A well-developed ISRM program aligns the responses to these questions with business strategies, helping to direct funding toward protective measures, deciding which risks to accept, and providing due diligence to regulators, customers, and company boards.
It also helps to understand what information security actually means. This field focuses on safeguarding data from unauthorized access, usage, disclosure, disruption, alteration, or destruction. Risk management aims to identify the necessary level of protection, where it should be applied, and what the costs will be.
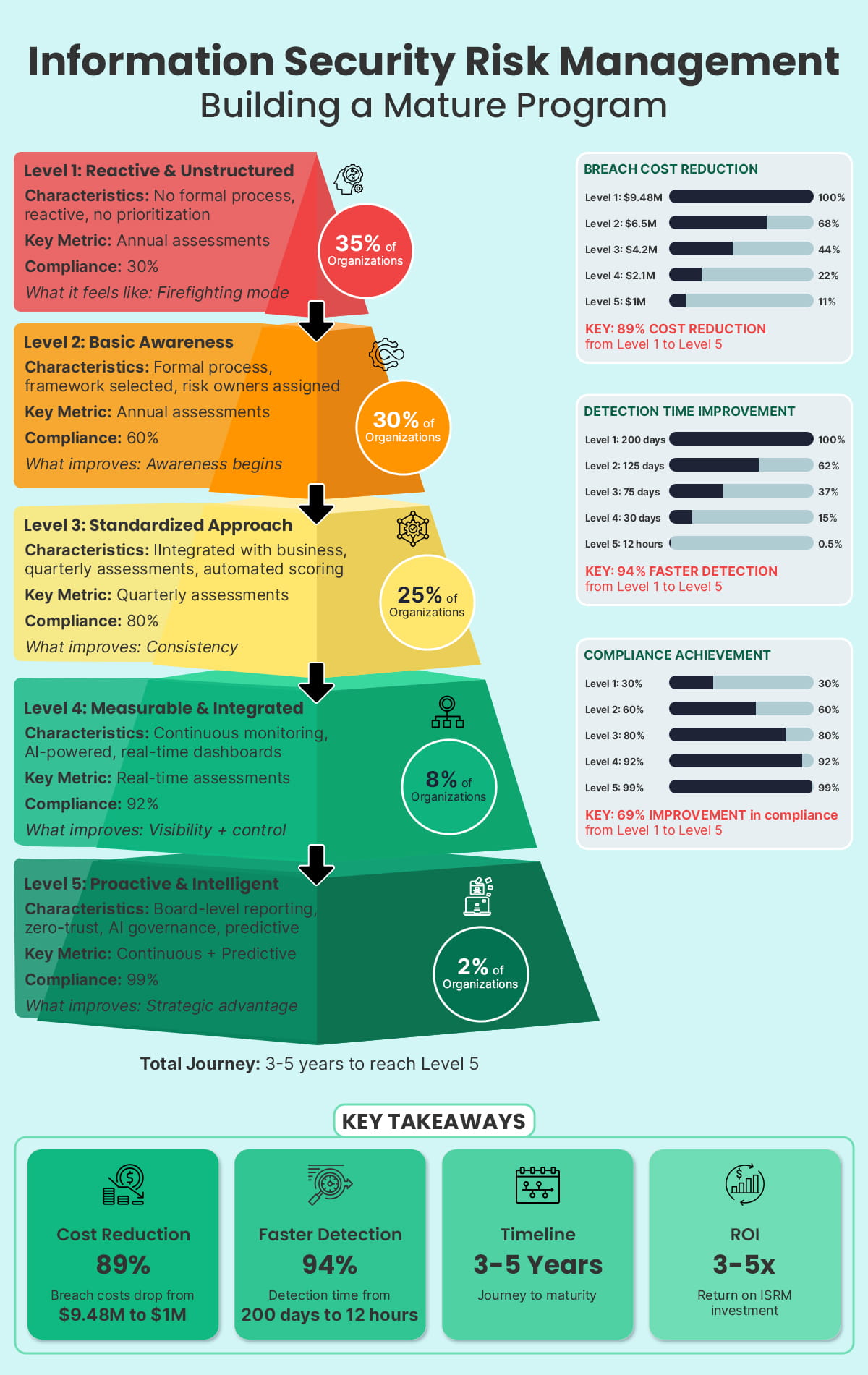
ISRM Maturity Levels
Understanding where your organization currently stands is just as important as knowing where it needs to go. ISRM maturity levels provide a structured benchmark that helps organizations evaluate the sophistication of their security risk program and identify clear areas for improvement. Progress across these levels directly translates into lower breach costs, faster threat detection, and stronger organizational resilience.
- Level 1: Ad-Hoc: No formal processes exist, and security decisions are entirely reactive.
- Level 2: Defined: Basic processes are documented but not yet consistently applied across the organization.
- Level 3: Managed: Security processes are actively monitored, reviewed, and managed with clear accountability.
- Level 4: Optimized: Security is proactive, data-driven, and continuously aligned with business objectives.
- Level 5: Strategic: Security risk management is fully embedded into business strategy and organizational governance.

The 5 Stages of Information Security Risk Management
Information security risk management is not something you set up once and walk away from. The following five stages are fundamental to the development of any effective Information Security Risk Management (ISRM) program:
Stage 1: Identify
Start by listing everything you need to protect: data, systems, applications, and third-party connections. You need to know what assets you have before you can assess risk. Also, identify any threats and vulnerabilities that could impact these assets.
Stage 2: Evaluate
After identifying the risks, the next step is to evaluate them. Consider how likely each threat is to occur and the severity of its potential impact. A straightforward scale of Low, Medium, or High is effective for most teams, for a more detailed approach, a quantitative model like FAIR can be utilized, which translates each risk into a specific financial figure.
Stage 3: Respond
Once you know your risks, decide what to do about each one. You can reduce it by putting controls in place, transferring it through cyber insurance, accepting it if it sits within your risk appetite, or avoiding it entirely by stepping away from the activity that creates it. Whatever you decide, write it down and assign someone to own it.
Stage 4: Track
Deploying controls is just the beginning. Use tools like SIEM, vulnerability scanners, and Key Risk Indicators to continuously verify that your defenses are performing as intended against real-world threats. Active monitoring is what keeps your risk program accurate and effective.
Stage 5: Review
Regularly check your risk register. New threats can emerge, operations can change, and regulations can update. Plan to review high-risk areas quarterly and the entire program annually to ensure your ISRM remains accurate and effective.

The Fundamental Objectives of Information Security
Before developing a risk management program, it is crucial to understand what you are protecting and why. The fundamental objectives of information security revolve around the CIA triad:
- Confidentiality: Ensuring information is only accessible to those who are authorized to see it
- Integrity: Ensuring data remains accurate, complete, and trustworthy at all times
- Availability: Making sure the right people can access the right information at the right time
These three principles serve as the foundation for every control decision, risk assessment, and treatment strategy in your Information Security Risk Management (ISRM) program. A risk that threatens confidentiality, such as a data breach, may be assessed differently from a risk threatening availability, like a Distributed Denial of Service (DDoS) attack, depending on your specific business context.
Some frameworks go beyond the CIA triad to include non-repudiation, which provides proof that an action occurred, and authenticity, which verifies the identity of users and systems. Both are particularly relevant in regulated industries and environments where digital transactions take place.
From Chaos to Control: The ISRM Maturity Journey and Business Impact
Why Information Security Risk Management Matters in 2026
Cyber threats have changed a lot in recent years. Ransomware is now handled by organized groups instead of individual hackers. These groups have structured operations and offer customer support and formal service agreements. Additionally, artificial intelligence has made it easier to launch advanced phishing campaigns on a larger scale. And supply chain vulnerabilities mean that one compromised vendor can put thousands of organizations at risk overnight. On top of that, regulators globally, from the EU’s NIS2 and DORA to the SEC’s cybersecurity disclosure rules, now require formal risk management programs as a baseline expectation.
Today’s CISO carries a very different set of responsibilities than before. Today, the CISO is no longer just a technical leader; they are expected to communicate risks in financial terms to the board, align security strategies with overall business objectives, and take responsibility for regulatory compliance. As a result, structured IT security risk management has moved from being solely an IT concern to a topic of discussion at the boardroom level.
Failing to manage risks can have serious financial consequences. In 2024 and 2025, data breach costs hit record highs. Insurers are raising premiums for organizations that cannot show they have strong security practices in place. For companies without a formal risk management program, the difference between what they spend and what they could lose is increasing.
The Information Security Risk Management Process
A structured information security risk management process follows five repeating stages. At its core, it forms the operational backbone of any serious information security management effort, giving teams a repeatable way to stay ahead of threats. Here is how each stage works in practice
1. Asset Identification and Classification.
The main idea of security risk management is simple: you cannot protect what you don’t know exists. Before creating a security strategy, organizations need to build a complete list of their assets, divided into three important categories.
- Data Assets: Customer PII, financial records, intellectual property, health data.
- System Assets: Servers, endpoints, cloud workloads, APIs, SaaS platforms.
- Third-Party Assets: Vendors with data access, open-source dependencies.
Once organizations catalog these assets, they must classify each one based on its CIA needs. For example, a database with customer payment information needs strict controls for confidentiality and integrity. However, a public marketing website may focus more on availability, with lower confidentiality requirements. This classification helps determine the acceptable risk for each asset and guides decisions in the risk management process.
2. Identifying Threats and Vulnerabilities.
Once organizations know what assets they have, they need to figure out what might go wrong and why. Threats are events or situations that can harm assets, while vulnerabilities are weaknesses that enable their exploitation.
In 2026, the biggest threats include ransomware, phishing attacks, internal security breaches, supply chain attacks, and AI-supported social engineering. This last threat is a rising concern because attackers use machine learning to deploy more manipulative and strategic attacks.
To find vulnerabilities, organizations should use various methods, including automated scanning tools, penetration testing, CIS-based configuration audits, and security awareness tests. They should also use established threat intelligence frameworks like MITRE ATT&CK and industry-specific ISACs. This ensures the threat model reflects actual attacker tactics rather than hypothetical scenarios.
3. Risk Assessment.
After identifying threats and vulnerabilities, the key question is: how serious is the risk? Risk is defined by the combination of the frequency of occurrence and the depth of its consequences. There are two main methods to assess this.
1- Qualitative assessment uses simple terms: Low, Medium, High, and Critical, to evaluate risk scenarios. It is fast, accessible for non-technical stakeholders to understand, and ideal for initial evaluations. A 5×5 risk matrix compares Likelihood against Impact to create clear risk ratings for each scenario.
2- Quantitative assessment, especially the FAIR (Factor Analysis of Information Risk) model, translates risk into financial terms. It calculates Annualized Loss Expectancy (ALE), showing the potential loss range with a certain probability. For example, there might be a 25% chance of losses between $1 million and $4 million in a year. CFOs, corporate boards, and cyber insurance underwriters increasingly want these financial details. Organizations that follow a recognized Risk Management Framework can provide consistent and auditable results.
For each identified risk, organizations should write down the threat scenario, the assets that are affected, the existing controls, the remaining risk level, and assign a risk owner, which is a key document for the entire Information Security Management program.
4. Risk Treatment
Assessment without action offers no protection. Once risks have been evaluated, organizations must select an appropriate response strategy from four recognized options:
Strategy | Description |
Mitigate | Apply controls that either make the risk less likely to occur or reduce the damage if it does. |
Accept | Formally document and tolerate the risk within defined appetite thresholds |
Transfer | Shift financial exposure through cyber insurance or contractual liability clauses |
Avoid | Eliminate the business activity that introduces the risk entirely |
Security controls are classified under three main categories:
- Technical controls.
- Administrative controls.
- Physical controls.
No single control guarantees complete protection. A multi-layered security approach guarantees that one compromised control does not trigger a devastating breach. It is also worth noting that Third Party Risk Management should factor into treatment decisions, particularly where vendors or external partners have access to sensitive systems or data.
5. Monitoring and Continuous Improvement.
Information security risks require persistent monitoring and attention. We cannot solve these problems once and forget about them. The threats change every day, new weaknesses are found, and changes in our business bring in new assets and areas that could be attacked. Additionally, rules and regulations continue to evolve. A resilient security program demands more than a one-time effort. Continuous monitoring through SIEM tools, Key Risk Indicators (KRIs), and scheduled risk register reviews keeps the organization informed and prepared at all times. Scheduled security exercises and penetration tests serve to verify that security controls function effectively in practical scenarios.
Organizations that embrace information security risk management as an ongoing discipline rather than a periodic exercise are far better positioned to detect threats early, respond swiftly, and prevent minor vulnerabilities from escalating into major incidents.
The organizations that withstand modern cyber threats are not necessarily those with the largest security budgets. They are those that embed security risk into their broader Enterprise Risk Management strategy, treating cyber risk with the same dedication and accountability applied to financial, operational, and regulatory risk.
Key Frameworks for Information Security Risk Management
The right framework provides a proven structure, regulatory credibility, and a common language across teams.
NIST Risk Management Framework (RMF)
The risk management framework developed by NIST is the most widely adopted in the United States, especially among government agencies and their contractors.
It follows six steps:
Categorize → Select → Implement → Assess → Authorize → Monitor.
The 2024 revision of NIST CSF 2.0 marked a significant shift by introducing a Governance function that formally positions risk management within organizational governance.
ISO/IEC 27005
ISO 27005 stands as the globally recognized standard for information security risk management, built to operate in close alignment with ISO/IEC 27001. Rather than enforcing a single methodology, it is recognized in regulatory frameworks across Europe, Asia-Pacific, and the Middle East. Any organization pursuing ISO 27001 certification must be able to demonstrate a structured risk management process rooted in ISO 27005 guidance.
FAIR (Factor Analysis of Information Risk)
FAIR is the leading quantitative framework, enabling organizations to model cyber risk in financial terms. It’s particularly powerful for justifying security investment, benchmarking against peers, and communicating with finance and executive leadership. Demand for FAIR practitioners has grown significantly as boards require dollar-denominated risk reporting.
Third-Party Risk Management
Third-party risk management has become one of the most critical and challenging components of ISRM. Organizations increasingly rely on vendors, SaaS platforms, cloud providers, and contractors, each of which can become a vector for attack.
A comprehensive third-party risk program should include the following components:
- Vendor risk questionnaires and security assessments are conducted before onboarding new vendors.
- Contractual security requirements and clauses that allow for auditing rights.
- Continuous monitoring of the vendor’s security posture.
- The requirement to secure a Software Bill of Materials from software providers.
- Defined responsibilities for incident notification and measurable SLA standards.
The SolarWinds attack, the MOVEit breach, and the XZ Utils compromise show that even trusted vendors can create serious risks. Starting in 2026, regulators, including the EU, will require clear programs to manage risks from third parties.
Enterprise Risk Management Integration
Enterprise risk management (ERM) is the broader organizational discipline that encompasses financial, operational, strategic, and compliance risks alongside cyber risk. Mature organizations integrate ISRM into their ERM program so that information security risk is weighted alongside other business risks in decision-making.
This integration matters for several reasons. It ensures cyber risk receives appropriate resource allocation relative to other priorities. It enables the board to view cyber risk in the same framework as financial or reputational risk. And it produces a unified risk language across the organization, which is critical when the CISO must communicate with the CFO, General Counsel, and CEO simultaneously.
When ISRM is siloed in IT, it tends to be underfunded and undervalued. When it feeds into ERM, it becomes a strategic asset.
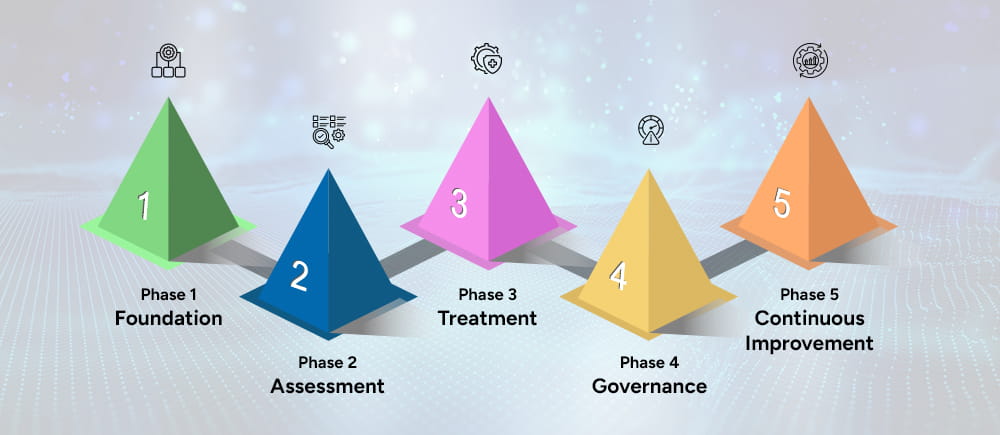
Building Your ISRM Program: Practical Roadmap
Phase 1 – Foundation: Get support from executives. Define how much risk the organization can accept. Choose a framework. Create an asset inventory.
Phase 2 – Assessment: Identify potential threats and vulnerabilities. Analyze risks and update the risk register. Assign risk owners in different business units.
Phase 3 – Treatment: Create a prioritized plan to address risks. Implement controls and track progress on remediation efforts.
Phase 4 – Governance: Set Key Risk Indicators (KRIs) and define reporting schedules. Form a risk committee and include risk management in procurement, change management, and software development.
Phase 5 – Continuous Improvement: Monitor controls continuously. Conduct tabletop exercises to test processes. Use lessons learned from incidents to update the risk register. Compare your organization’s practices with peers annually and update frameworks as needed.
How to Measure Your ISRM Program
To manage IT security risks effectively, focus on measuring results rather than just activities. Here are key metrics to track:
- Mean Time to Detect and Mean Time to Respond are two critical performance indicators.
- Number of open critical/high vulnerabilities and days-to-patch.
- Percentage of assets with current risk assessments.
- Third-party vendors with completed risk reviews.
- Risk register coverage: % of risks with accepted treatment plans.
- Phishing simulation click rates and security training completion.
Executive and board reporting should always translate these into business impact, financial exposure, regulatory risk, and operational disruption, rather than raw vulnerability counts.
Conclusion
Information security risk management (ISRM) is the foundation on which all security efforts are built. Without it, organizations pour resources into security measures with no certainty that they are targeting the right risks.
When ISRM is in place, security becomes a well-organized, measurable part of the business that protects assets, meets regulatory requirements, and earns the trust of customers and partners.
By 2026, organizations that view ISRM as an ongoing priority for the board, rather than just a yearly task for IT, will build true resilience. The process doesn’t have to be perfect from the beginning. It just needs to begin and get better over time.
Let’s ensure that your Information security risk management is done right, with the team here at Amsat.
Frequently Asked Questions
What is the difference between ISRM and IT risk management?
IT risk management focuses on technology-related risks such as system failures and infrastructure outages. ISRM takes a broader view, encompassing the confidentiality, integrity, and availability of all information assets regardless of where they reside. ISRM is a business discipline; IT risk management is a technical function.
How often should organizations conduct risk assessments?
A formal risk assessment should be conducted at least annually. Assessments should also be triggered by significant business changes such as mergers, system deployments, or following a security incident. High-risk environments may warrant more frequent reviews.
What is the typical cost of implementing ISRM?
Costs vary depending on organizational size and maturity. Small businesses can establish a foundational program using free frameworks such as NIST CSF or CIS Controls. Larger enterprises typically invest in GRC platforms and specialized personnel. The more relevant question is not what ISRM costs, but what a poorly managed risk event would cost without it.
How does ISRM relate to ISO 27001 compliance?
ISRM is not merely complementary to ISO 27001 compliance; it is a prerequisite. Organizations pursuing certification must conduct structured risk assessments, maintain a risk register, and demonstrate that treatment decisions are informed by documented risk evaluations aligned with ISO 27005.
Can small businesses implement ISRM effectively?
Small businesses can begin with a lightweight qualitative risk assessment aligned to a practical framework such as NIST CSF or CIS Controls. A simple risk register maintained in a spreadsheet is a perfectly adequate starting point. What matters most is not the sophistication of the program but the consistency with which it is practiced.
TAGS
- Cyber Security
- Penetration Testing