Latest Blogs

By AMSAT Aug 25,2023
Penetration Testing: How to Protect Your Systems from Attack
In today’s increasingly interconnected world, businesses and organizations of all sizes are vulnerable to cyber-attacks. These attacks can range from simple phishing scams to sophisticated data breaches, and they can have a catastrophic impact on a company’s operations and bottom line.
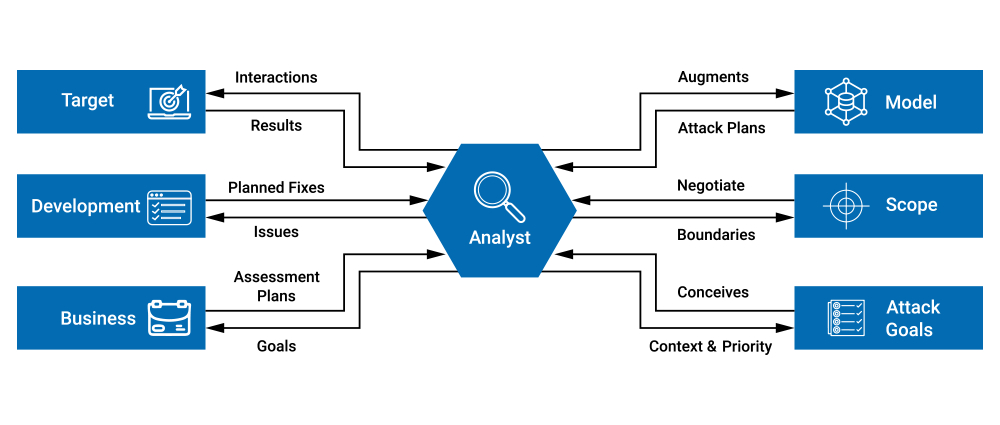
One of the best ways to protect your systems from attack is to conduct regular penetration testing. Penetration testing is a simulated attack on your systems and networks by a qualified security professional. The goal of penetration testing is to identify and exploit vulnerabilities in your security so that they can be fixed before they are exploited by real attackers.
There are many different types of penetration testing, but they all follow a similar process:
- Planning: The first step is to plan the testing. This involves identifying the scope of the testing, including the systems and networks that will be tested.
- Recon: The next step is to gather information about the target systems and networks. This information can be gathered through a variety of methods, such as social engineering, network scanning, and vulnerability scanning.
- Exploitation: The third step is to exploit the vulnerabilities that have been identified. This may involve using a variety of techniques, such as password cracking, SQL injection, and cross-site scripting.
- Reporting: The final step is to report the results of the penetration test to the organization. This report should include a detailed description of the vulnerabilities that were found, as well as recommendations for how to fix them.
Why Penetration Testing is Important
Penetration testing is an essential part of any organization’s cybersecurity strategy. By conducting regular penetration testing, you can identify and fix vulnerabilities in your security before they are exploited by attackers. This will help to protect your systems from attack and keep your data safe.
Penetration testing can enhance your security strategy in a number of other ways. One key advantage is its function to assure adherence to industry regulations. Several industries, notably healthcare and finance, are required by law to regularly undergo security testing. Additionally, penetration testing makes a considerable improvement to your overall security posture. Your systems can be strengthened, reducing their susceptibility to possible attacks, by identifying vulnerabilities and fixing them. This practice also helps with risk detection and efficient risk mitigation. Gaining awareness of potential threats to your systems will allow you to take proactive action to lower the risks and decrease the likelihood of successful attacks.
If you are concerned about the security of your systems, penetration testing is a valuable tool that can help you to protect them from attack. By conducting regular penetration testing, you can identify and fix vulnerabilities before they are exploited by attackers, and you can improve your overall security posture.
Factors to Consider Before Choosing a Company
When selecting a penetration testing company, it’s essential to consider a few key factors. First and foremost, prioritize companies with a wealth of experience and a proven history of successful engagements. Seeking referrals from other organizations that have previously worked with the company can provide valuable insights into their capabilities.
Additionally, ensure that the chosen company understands your unique needs and prerequisites, fostering effective collaboration. It’s also advisable to secure a written agreement detailing the testing’s scope, anticipated deliverables, and associated costs. This holistic approach will help make an informed decision and establish excellent collaboration with the selected penetration testing company.
Conclusion
Penetration testing strengthens your systems by spotting flaws before criminal actors can take advantage of them, serving as a vital defense mechanism against possible cyber-attacks.
Take into account the given suggestions when choosing a reliable partner to help you improve your security posture. Examine the company’s credentials, experience, and track record. Prioritize collaboration and transparent communication to establish a customized strategy. Check the thoroughness of their procedures and resources, and examine their post-assessment advice and support.
These recommendations may help you easily select a reliable penetration testing company, protecting your digital assets and enhancing your resilience against developing cyber risks.
TAGS
- Cyber Crime
- Penetration Testing
Recent Blogs
Ready to Get Started?
Our specialists are ready to tailor our security service solutions to fit the needs of your organization.