By AMSAT March 22, 2026
XDR vs SIEM vs SOAR: Which Security Platform Does Your Enterprise Actually Need?
Your SOC team is drowning. Thousands of alerts pour in every day, analysts are overburdened, and threats are growing more sophisticated by the hour. In response, vendors have produced three distinct categories of security platforms: XDR vs SIEM vs SOAR, each promising to fix the problem. The challenge? They overlap, they complement each other, and they are too often confused for one another.
If you are a security director, CISO, or SOC manager trying to decide which platform between XDR vs SIEM vs SOAR, your enterprise actually needs, or how to make the ones you already own work together, the answers are right here.
What you’ll learn:
- What XDR vs SIEM vs SOAR are and how each one fits into a modern enterprise security operation
- How each platform works under the hood, from log collection and alert generation to automated response and cross-domain detection
- The core capabilities and key limitations of each tool, so you know exactly what you’re getting and what you’re not.
- How SIEM and SOAR work together, and why one without the other leaves critical gaps in your security operations
- Whether XDR can replace SIEM or SOAR, and the honest answer to that question
- A head-to-head comparison of all three platforms across six critical dimensions, including detection method, compliance value, and automation level
- A practical decision framework to help you determine which platform your organization should prioritize first
- How XDR vs SIEM vs SOAR layer together into a unified SOC architecture for mature security teams
What Is XDR? (Extended Detection and Response)
Between XDR vs SIEM vs SOAR, think of XDR as the evolution of endpoint detection and response (EDR), but expanded across your entire attack surface. So, when talking about XDR vs. EDR, between the two, EDR focuses entirely on endpoints such as laptops and servers, XDR goes further and pulls telemetry from a range of traditionally siloed monitoring systems, including email security, network detection, cloud workloads, and identity platforms. How XDR works: XDR ingests and correlates security data from multiple sources onto a single platform, enabling analysts to detect threats that span different attack vectors. A threat that begins as a phishing email, pivots through an endpoint, and exfiltrates via a cloud resource would be nearly invisible in a siloed environment; XDR surfaces it as a unified incident.Core XDR Capabilities
- Collect and analyze data from endpoints, cloud workloads, networks, and email using AI and machine learning.
- Prioritize events and deliver insights in a normalized format through a single unified console.e
- Automate complex, multi-step response actions, isolating infected hosts, blocking malicious IPs, and remediating vulnerabilities
- Reduce alert fatigue by suppressing false positives through cross-domain behavioral context.
- Available in two forms: Native XDR and Open/Hybrid XDR (best-of-breed integrations)
XDR’s Key Limitation
XDR is purpose-built for threat detection and response. It does not natively address log management for compliance, non-threat data analysis, or the deep workflow orchestration that mature SOC teams rely on. This is why XDR cannot fully replace either SIEM or SOAR, but it fills a critical gap between them.What Is SIEM? (Security Information and Event Management)
SIEM is the oldest of the three platforms (XDR vs SIEM vs SOAR) and, for many enterprises, the foundation of their security operations. A SIEM collects, normalizes, and stores log data from across your entire environment, operating systems, firewalls, applications, network devices, and cloud services into one centralized repository. How SIEM works: Log data is parsed and indexed so security analysts can search, correlate, and query it. SIEMs perform log correlation to detect relationships between events and help you in advanced threat detection. For example, a failed login attempt correlated with a subsequent file access from the same IP address can signal a brute-force attack in progress. Alerts are surfaced to security personnel for investigation.Core SIEM Capabilities
The use cases of SIEM are countless, but the basics are:- Collect and normalize log data from every corner of the environment: hardware, software, and cloud.
- Correlate events across disparate sources to identify security incidents and anomalies
- Generate alerts, dashboards, and reports for security teams to investigate
- Enable compliance reporting for frameworks such as PCI-DSS, HIPAA, SOX, and GDPR
- Support forensic investigation with long-term log retention and historical querying
SIEM’s Key Limitation
SIEM is primarily a detection and logging tool; its native response capabilities end at generating an alert. It cannot take automated action on threats. That is SOAR’s job. Additionally, SIEM produces a high volume of alerts, many of which are false positives, creating alert fatigue for SOC analysts without additional filtering or automation layered on top.What Is SOAR? (Security Orchestration, Automation and Response)
If SIEM is the alarm system that detects and logs every security event, SOAR is the response team that acts on it. SOAR platforms take in data from many sources, including but not limited to SIEM, and enable automated, orchestrated responses to security incidents through pre-built and custom playbooks. How it works: When a SIEM (or another security tool) generates an alert, SOAR ingests that alert and triggers a playbook, a series of automated response actions. These can include enriching the alert with threat intelligence, sending Slack notifications to on-call analysts, quarantining a suspicious endpoint, blocking a malicious IP, or opening a ticketing record in Jira. Human analysts are brought in only for complex decisions that require judgment.Core SOAR Capabilities
- Automate routine incident response tasks through customizable playbooks, dramatically reducing mean time to respond (MTTR)
- Orchestrate communication between disparate security tools that don’t natively talk to each other
- Centralize case management, tracking incidents from detection through resolution in one interface.
- Apply machine learning to predict and categorize future threats based on historical patterns.
- Generate metrics on response efficiency, enabling SOC teams to demonstrate ROI
SOAR’s Key Limitation
SOAR does not collect or analyze raw log data on its own; it depends on SIEM (or XDR) for its data input. Implementing SOAR effectively also requires a relatively mature SOC: you need defined playbooks, experienced analysts who can build and tune automation workflows, and a set of integrated tools. SOAR in an immature security environment can add complexity without benefit.The Key Differences Between SIEM, SOAR, and XDR
SIEM vs. SOAR
SIEM and SOAR are designed to work together. SIEM is the data backbone; it aggregates and analyzes log data and surfaces alerts. SOAR is the action layer; it takes those alerts and automates the response. The combination of SIEM and SOAR is powerful: security teams can focus on high-priority investigations while SOAR handles the mechanical, repeatable tasks that would otherwise consume hours of analyst time.| Features | SIEM | |
|---|---|---|
| Primary Function | Log collection, correlation, and alerting | Incident response automation and orchestration |
| Data Source | Collects directly from systems, apps, and network devices | Ingests from SIEM, threat intel feeds, ticketing systems, and more |
| Response Capability | Generates alerts only, no automated action | Executes automated playbooks and response workflows |
| Compliance Role | Strong, long-term log retention and audit trails | Minimal, focused on operational efficiency, not compliance |
| Ideal For | Compliance-heavy orgs needing forensic and audit capability | Mature SOCs seeking to reduce alert fatigue and MTTR |
| Works Without the Other? | Yes, but the response is manual and slow | No, SOAR needs a data source (SIEM or XDR) to function |
SIEM vs XDR
XDR and SIEM both detect threats, but they do so very differently. SIEM relies on log correlation across massive data sets; it is broad but can be noisy. XDR uses machine learning and cross-domain behavioral analytics to correlate telemetry natively, producing fewer, higher-fidelity alerts. However, XDR cannot replace SIEM’s compliance and log management capabilities.| Features | XDR | SIEM |
|---|---|---|
| Detection Method | ML-driven, cross-domain behavioral analytics | Rule-based log correlation with some ML plug-ins |
| Data Scope | Endpoint, network, email, cloud, identity, natively unified | Broad but siloed, collects logs from everywhere independently |
| Alert Quality | High fidelity, fewer false positives due to context | High volume, noise requires significant tuning |
| Compliance | Not designed for compliance reporting or log retention | Core strength, purpose-built for audit and compliance |
| Response | Built-in automated response across the security stack | Alerts only, no native response automation |
| Implementation | Faster to value, unified platform | Complex, requires tuning, integrations, and ongoing rule management |
XDR vs SOAR
XDR includes lightweight, built-in response automation, which can isolate a host, block an IP, or quarantine a file automatically. SOAR goes much deeper: it orchestrates complex, multi-tool workflows, manages case lifecycles, and integrates with virtually any security or IT tool in your stack. Think of XDR automation as a built-in first-aid kit, and SOAR as a fully equipped emergency response team.| Features | XDR | SOAR |
|---|---|---|
| Automation Type | Native micro-automation within its own platform | Cross-tool orchestration via custom playbooks |
| Integration Depth | Integrates with its own vendor ecosystem and key third parties | Integrates with virtually any security or IT tool |
| Playbook Complexity | Pre-built, limited customization | Fully customizable, complex multi-step workflows |
| Case Management | Basic incident tracking | Full SOC case management with SLA tracking |
| Data Dependency | Self-sufficient, generates its own detections | Requires a data source (SIEM or XDR) to trigger playbooks |
| Best For | Unified detection and fast automated response | Complex orchestration across a diverse tool ecosystem |
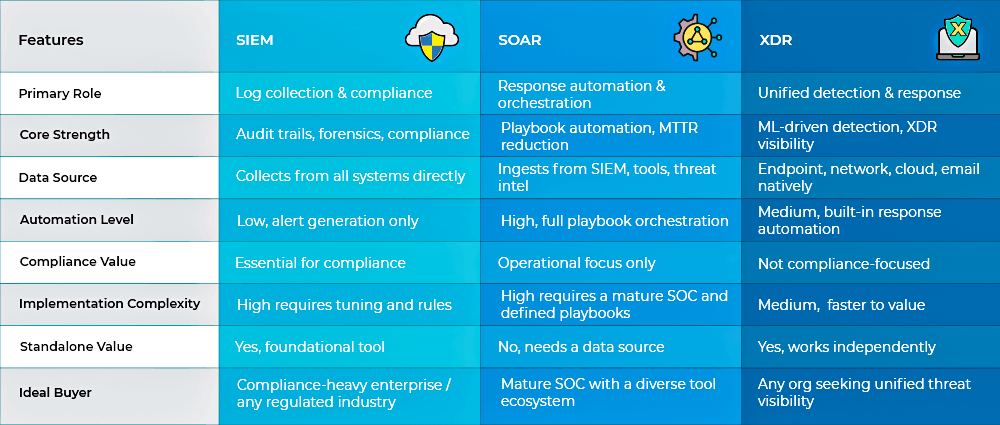
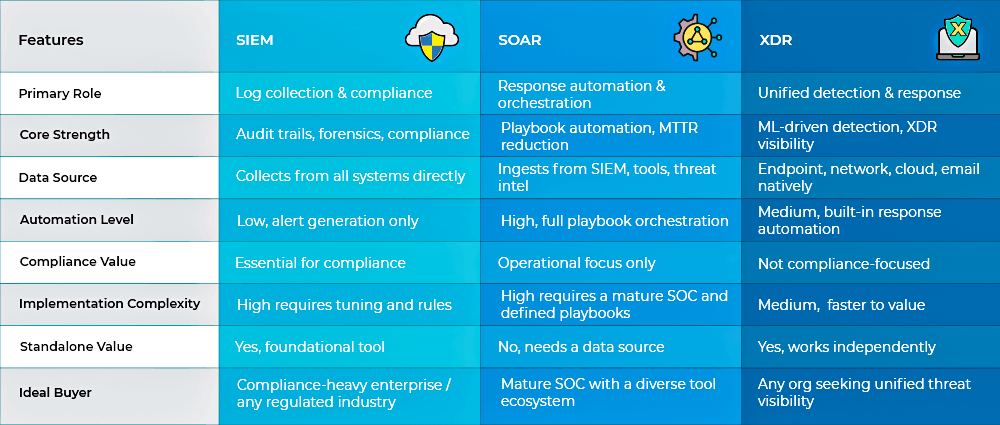
The Complete XDR vs SIEM vs SOAR Comparison
Which Security Platform Does Your Enterprise Actually Need?
Choosing the right security platform is less about which tool is best between XDR vs SIEM vs SOAR and more about what your organization actually needs right now. Your team size, SOC maturity, compliance obligations, and existing tools all play a role in that decision. Here is a practical way to think through it. SIEM is the right choice for organizations that are:- Operating in a regulated industry like healthcare, finance, government, or legal, where audit trails aren’t optional.
- Working within compliance frameworks such as PCI-DSS, HIPAA, SOX, or GDPR, and need to demonstrate security controls to regulators.
- Retaining long-term logs and forensic investigations as part of the security requirements
- Building security operations from the ground up and need a solid data foundation before anything else.
- Demonstrating accountability to auditors and stakeholders as a regular part of your security responsibilities.
- SIEM is producing more alerts than your analysts can realistically keep up with
- A significant portion of your incidents are repetitive and high-volume, think phishing triage, IP blocking, and account lockouts
- Your security tools are growing, but aren’t communicating with each other effectively.
- Your team has defined playbooks or the capacity to build them. SOAR gives the most back to teams that have already done the process work
- Reducing response time and proving SOC efficiency to leadership has become a priority.
- Threats are slipping through because they span multiple environments, endpoint, network, email, and cloud, and your current tools aren’t connecting the dots.
- Your SIEM alert volume has become more noise than signal, and tuning rules aren’t keeping up.
- You want faster, more accurate detection without the overhead of managing complex rule sets.
- You’re a mid-market organization that needs strong visibility without the resources to run a large, multi-tool SOC.
- Built-in automated response matters to you, and standing up a separate SOAR platform isn’t practical right now.
- SIEM serves as the foundation, bringing together and organizing logs from across the entire environment while handling compliance and retaining data for regulatory and forensic purposes.
- XDR sharpens detection, sitting above SIEM as the primary detection engine, correlating telemetry across endpoint, cloud, email, and network using machine learning to catch what rule-based systems miss
- SOAR closes the loop, orchestrating the response layer, running playbooks that handle routine incidents automatically, and escalating the complex ones to senior analysts who actually need to be involved
Conclusion
When we talk about XDR vs SIEM vs SOAR, they are not competing platforms. There are three layers of the same answer to a problem every security team faces: too many threats, too little time, and too much noise. SIEM gives you the foundation. It keeps the logs, satisfies the auditors, and makes sure nothing gets lost. XDR gives you intelligence. It connects the dots across your environment and surfaces the threats that siloed tools miss. SOAR gives you speed. It handles the repetitive work automatically so your analysts can focus on the incidents that actually need human judgment. Start with what solves your most pressing problem. Build from there. With the best Security Threat Detection, Incident Response and Forensics team, you can make sure every tool you add is making your team sharper, not just your stack longer. Let’s ensure your security stack is built right, with the team here at Amsat.Frequently Asked Questions
What is the difference between SIEM and SOAR?
SIEM is a log collection and analysis platform that detects threats and generates alerts. SOAR is a response automation platform that acts on those alerts. SIEM identifies what is happening; SOAR decides and executes what to do about it. They are designed to complement each other: SIEM provides the data, SOAR provides the response.Can XDR replace SIEM?
Partially, but not fully. XDR can replace SIEM for threat detection purposes, using cross-domain behavioral analytics to identify threats more accurately than SIEM’s rule-based approach. However, XDR cannot replace SIEM’s log management, compliance reporting, or long-term data retention capabilities. Organizations with compliance requirements will still need SIEM alongside XDR.What is SOAR in Cyber Security?
SOAR, which stands for Security Orchestration, Automation, and Response, is built to do one thing exceptionally well: act fast. Rather than waiting on analysts to manually work through every alert, it automates repetitive security tasks like phishing investigation, IP blocking, and user account suspension through pre-defined playbooks. SOAR reduces the mean time to respond to incidents and allows security teams to scale their capacity without hiring additional analysts.Is XDR the same as SOAR?
While XDR and SOAR both bring automation to the table, they are not the same thing. XDR handles lightweight automation within its own platform, covering actions like isolating hosts and blocking IPs. SOAR goes significantly deeper, orchestrating complex workflows across all your security tools through fully customizable playbooks and centralized case management. The two complement each other far better than they compete.Which is better: XDR vs SIEM vs SOAR?
Each platform excels in a different area, and the right choice really comes down to where your organization is today. SIEM leads on compliance and forensics, SOAR on response automation, and XDR on unified threat detection. Most mature enterprises find that deploying all three together delivers the most complete coverage.Can I use SIEM and XDR together?
Many security teams are already running both, and for good reason. XDR brings high-fidelity detection to the table while SIEM handles compliance and forensic investigation in the background. Together, they reduce alert volume, improve SOC efficiency, and take a significant amount of tuning overhead off your team’s plate.TAGS
- Cyber Security
- Penetration Testing
Recent Blogs
Saima Naz
Mar 26 2026
-
Category:
Saima Naz
Jan 30 2026
-
Category:
Saima Naz
Dec 31 2025
-
Category:
Saima Naz
Sep 30 2025
-
Category: